An Ultra-Low Power Wide-Band Single-Transistor Second-Order Allpass Filter in 65nm CMOS
In this paper, we propose a MOS design of a second-order voltage-mode allpass filter to be used as a time delay cell. The proposed filter is based on a single transistor, three resistors and two energy storage elements and was designed in a 65nm CMOS technology. Post-layout simulations demonstrate a group delay of approximately 13ps across a 30GHz bandwidth, while only consuming 809.7μW from a 1-V supply. As a proof of concept, the proposed filter was constructed and verified experimentally using discrete MOS transistors. The experimental results show a group delay of approximately 370ns
Single-Transistor Second-Order Allpass Filters
This paper presents two CMOS designs of a second-order voltage-mode allpass filters (APFs) for high-frequency applications. Each of the proposed filters is based only on a single transistor and four surrounding impedances. The first proposed allpass filter is an RL filter while the second proposed one is an RLC filter. A detailed analysis along with the parasitic effects is provided for each of the proposed filters. As a proof of concept, one design was constructed and verified experimentally using discrete MOS transistors at a 2.3MHz pole frequency. The experimental results showed a group
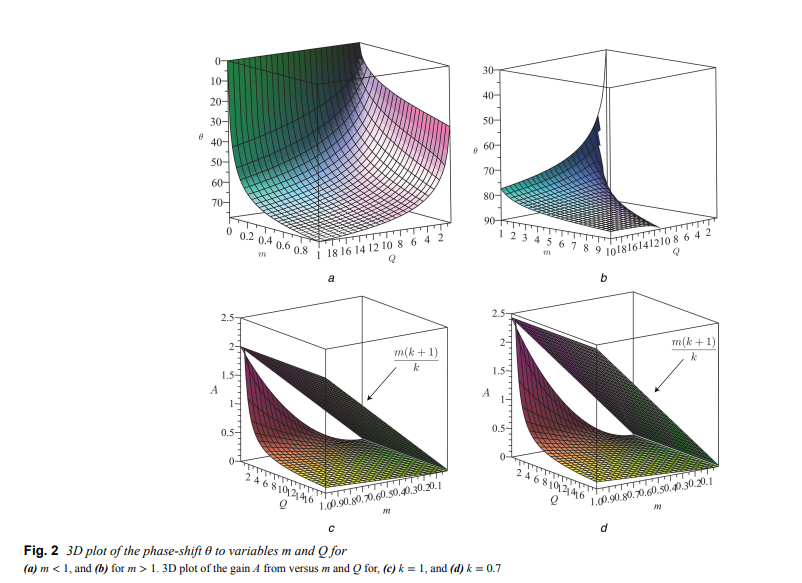
Third-order tunable-phase asymmetric crosscoupled oscillator
Here, the authors show that an asymmetric cross-coupled oscillator can be used to achieve independent-phase tunable outputs. In particular, a third-order cross-coupled oscillator, with non-balanced loads, is studied and expressions for its start-up condition, oscillation frequency, phase-shift between its two outputs as well as their amplitude ratio are derived. From these expressions, it is found that independent tuning of these design specifications is possible and a voltage-controlled phasetunable oscillator can be achieved. As a consequence of the non-balanced loads, the tail biasing
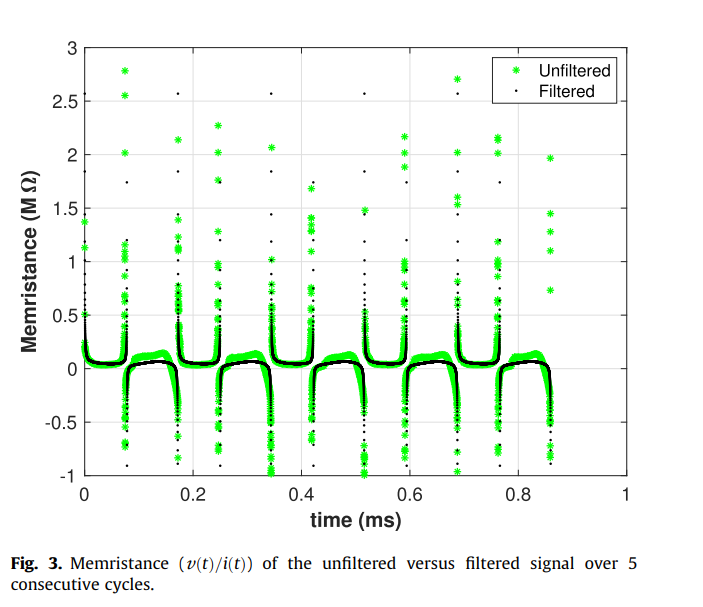
On the mechanism of creating pinched hysteresis loops using a commercial memristor device
In this short communication we analyze the impact of signal harmonics on the formation of the pinched hysteresis loop using a commercial memristor device. We show that by using only the fundamental frequency and the second harmonic components, extracted from the measured electrical current signal, a distortion-less pinched hysteresis loop is re-created. This loop is then used to simulate memristor-based AND/OR gates without any loss in digital functionality. This verifies that the generation of a pinched hysteresis loop requires a nonlinear frequency doubling mechanism to create a second
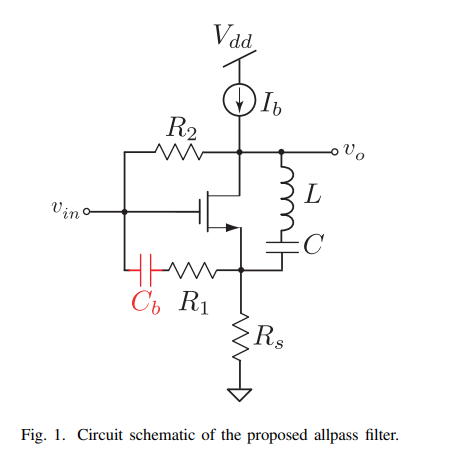
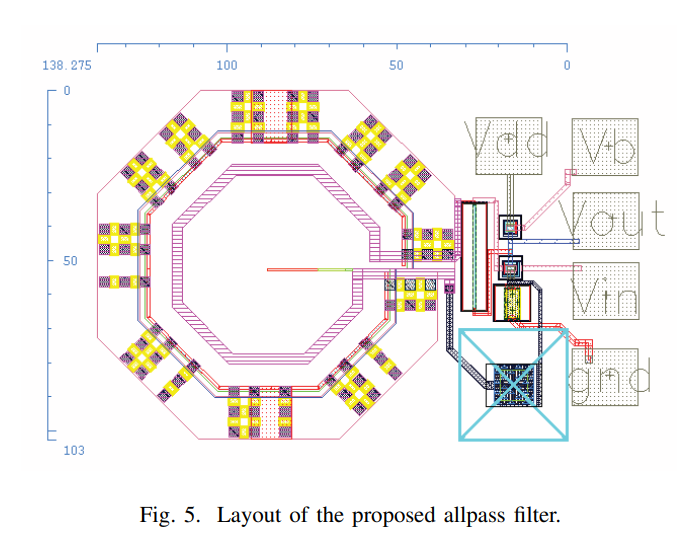
8-GHz low-power voltage-mode second-order allpass filter in 65-nm CMOS
In this paper, a CMOS wide-band low-power second-order voltage-mode allpass filter design is proposed as a true time delay element. The proposed allpass filter core design consists of a single transistor, three resistors, one capacitor and one inductor. As a time delay element, the proposed circuit exhibits a group delay of 34 ps within a bandwidth of 8 GHz while consuming only 926 μW from a 1-V supply voltage. The proposed filter was designed in 65-nm CMOS technology and verified through post-layout simulation results. © 2019 IEEE.
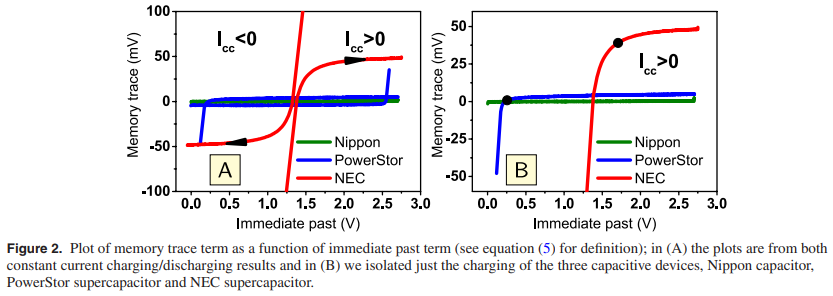
Quantification of memory in fractional-order capacitors
In this study we quantify and interpret the inherent memory in fractional-order capacitors when subjected to constant current charging/discharging waveforms. This is done via a finite difference approximation of the fractional order rate equation I(t) = Cαdαv(t)/dtα (0 le; α ≤ 1) relating current to voltage in these devices. It is found that as the fractional exponent α decreases, the weight of the voltage memory trace that results from the contribution of past voltage activity increases, and thus the measured response of the device at any time is increasingly correlated to its past. Ideal
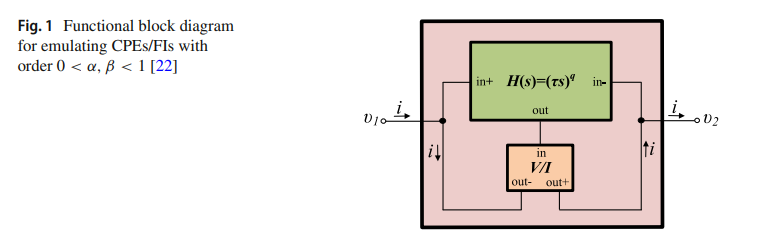
Generalized Fully Adjustable Structure for Emulating Fractional-Order Capacitors and Inductors of Orders less than Two
A novel scheme suitable for the emulation of fractional-order capacitors and inductors of any order less than 2 is presented in this work. Classically, fractional-order impedances are characterized in the frequency domain by a fractional-order Laplacian of the form s± α with an order 0 < α< 1. The ideal inductor and capacitor correspond, respectively, to setting α= ± 1. In the range 1 < α< 2 , fractional-order impedances can still be obtained before turning into a Frequency- Dependent Negative Resistor (FDNR) at α= ± 2. Here, we propose an electronically tunable fractional-order impedance
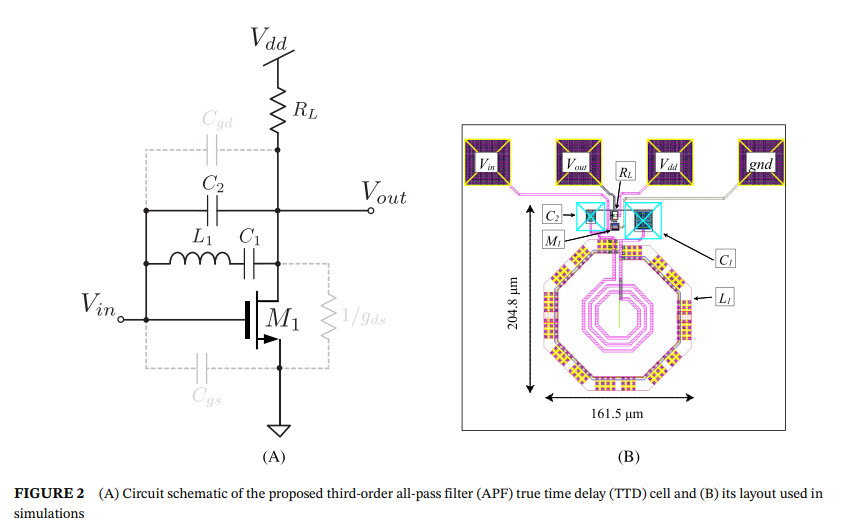
Wideband third-order single-transistor all-pass filter
In this letter, a third-order wideband voltage-mode all-pass filter (APF) is proposed for application as a true time delay (TTD) cell. The advantages of designing a single-stage higher order filter over cascading several lower order stages are illustrated. The proposed APF circuit is based on a single metal-oxide-semiconductor (MOS) transistor and is canonical because it requires one resistor, one inductor, and two capacitors. To the best of the authors' knowledge, this is the first single-transistor third-order APF circuit to be reported in the literature. The operation of the proposed APF is
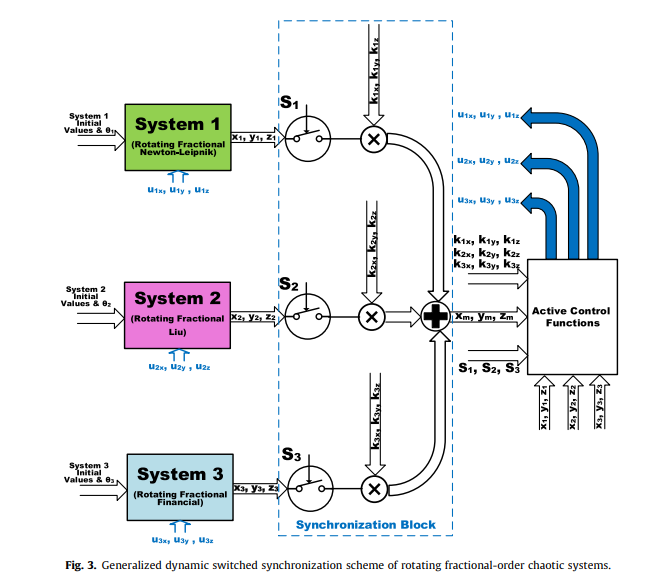
Generalized switched synchronization and dependent image encryption using dynamically rotating fractional-order chaotic systems
This paper presents a generalization, attractor control and multi-scroll generation method for fractional-order chaotic systems through rotation transformation. A novel synchronization-dependent colored image encryption and secure communication scheme is also proposed. The systems with dynamic rotation angle fit successfully in a generalized dynamic switched synchronization scheme. Dynamic control switches specify whether the system acts as a master or slave. Dynamic scaling factors determine whether the master is a single system or a combination of two or more systems. Simulation results
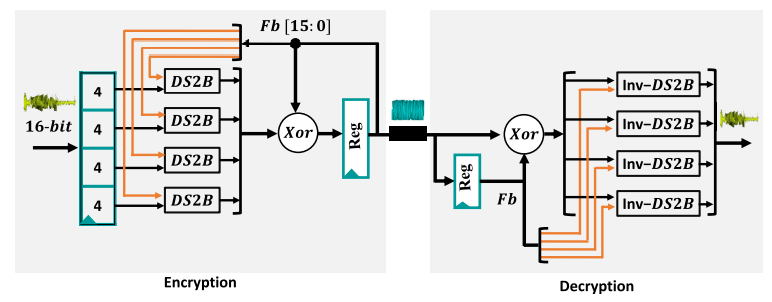
DS2B: Dynamic and Secure Substitution Box for Efficient Speech Encryption Engine
This paper proposes an efficient encryption technique based on Dynamic and Secure Substitution Box (DS2B) design suitable for IoT and resource-constrained platforms. The DS2B has the advantages of simple structure and good encryption performance. A different number of strong S-boxes could be generated with minor variations in the DS2B parameters. Performance analyses of the DS2B, including differential/linear cryptanalysis, bijective, nonlinearity, strict avalanche criterion (SAC), and bit independence criterion (BIC) have been presented where high nonlinearity , and low differential
Pagination
- Previous page ‹‹
- Page 13
- Next page ››
